Hello everyone, in this article I will give you information about the Task Scheduler, which was created to ensure persistence on Windows Systems. Let’s start. 🙂
Scheduled Tasks are available on all Windows operating systems. It is simple to use and most users are not aware of the existence of scheduled tasks. Therefore, it is a very good weapon for attackers. Most people working in this field do not know which applications are normal or abnormal when loading operating systems.
Task Scheduled
Scheduled tasks keep a task or job running periodically. Or a command to be executed when certain events occur are program files. For example; “Run every time the computer boots up.” or “Run at 8:00 every Monday. Users such as system administrators use scheduled tasks to automatically create and run tasks.
Ensuring persistence in the target system is the most important goal of the enemies. If the attackers cannot establish persistence in the target system, they have to repeat the first access tactics every time. Enemies also use the task scheduler utility of their operating system to ensure persistence on the target system.
Persistence
Persistence is the techniques used by attackers to maintain their access to target systems. In this context, persistence includes access and configuration to maintain the initial foothold of the systems.
You can access the persistence techniques in the ATT&CK matrix from this link.
One of the most famous persistence techniques is creating a scheduled task that will execute within a time range to execute the target code.
For example, let’s examine the scheduled task created by an attacker group;
- schtasks /create /tn “persistenttask” /tr C:\Users\Public\example.exe /sc ONLOGON /ru “System”
/tn – Specifies a name for the task.
/tr – Specifies the program or command that the task runs.
/sc – Specifies the schedule type.
/ru – Runs the task with permissions of the specified user account.
Creating a Task Scheduler in Windows
To create a task scheduler, I will do the following:
- First, I will specify a service that I want to start automatically when the computer boots up.
- Then I will write a simple Batch script.
- Finally, I will make the work start automatically via the Schedular Task.
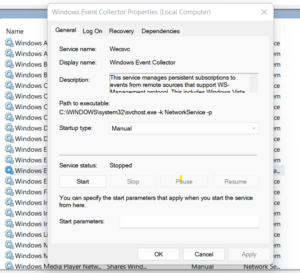
Now I go to the “Services” tab to specify my service. Here I specify my “Windows Event Collector” service. Here I detect that the service I selected does not start automatically. That’s why I choose this service.
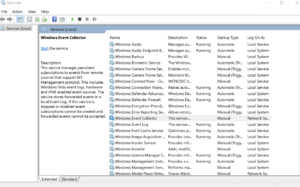
At the same time, I see that the status of the service I selected is stop.
We have set it to our service and we have completed the first step. Now we can start writing a simple Bacth script.
Now I stop the service first and then start it with batch script. Then I save the script I wrote in the automated folder with the extension “.bat”.

And now we come to the Task Scheduler interface. Here we create a new task by saying “right click-new task”.

Event IDs covering scheduled tasks:
- Event ID 4698 – A scheduled task was created: This event generates every time a new scheduled task is created.
- Event ID 4699 – A scheduled task was deleted: This event generates every time a scheduled task was deleted.
- Event ID 4700 – A scheduled task was enabled: This event generates every time a scheduled task is enabled.
- Event ID 4701 – A scheduled task was disabled: This event generates every time a scheduled task is disabled.
- Event ID 4702 – A scheduled task was updated: This event generates every time scheduled task was updated/changed.
- Event ID 4688 – A new process has been created: This event generates every time a new process starts.
- Event ID 5145 – A network share object was checked to see whether client can be granted desired access: This event generates every time network share object (file or folder) was accessed.


